Linux Curl with Proxy
Linux Curl with Proxy
What is Curl? curl is a tool to transfer data from or to a server, using one of the supported protocols (DICT, FILE, FTP, FTPS, GOPHER, HTTP, HTTPS, IMAP, IMAPS, LDAP, LDAPS, POP3, POP3S, RTMP, RTSP, SCP, SFTP, SMB, SMBS, SMTP, SMTPS, TELNET and TFTP). The command is designed to work without user interaction.
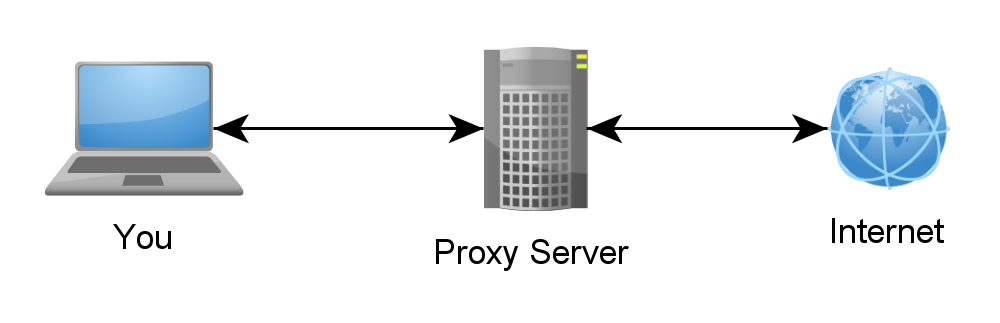
So in the cloud you may find yourself on a server that needs to communicate to an external system but it isn’t allowed to go there directly. In which case you will most likely have a proxy server to communicate through. In PeopleSoft you can define a web gateway proxy server, however, to test to make sure that the server is working correctly with the proxy you will want to do a curl test.
Linux Command Prompt –> curl http://whatsmyip.com
This should return the external IP address of the system you are coming out of. If this returns nothing you are likely blocked from going to that address. So to push the request through the proxy server, you need to set the proxy in an environment variable:
Linux Command Prompt –> export http_proxy=http://myproxy.atmyserver.com:80
Linux Command Prompt –> curl http://whatsmyip.com
Now as long as the proxy is allowed to communicate to that address you should see the IP address of the system you are communicating from.